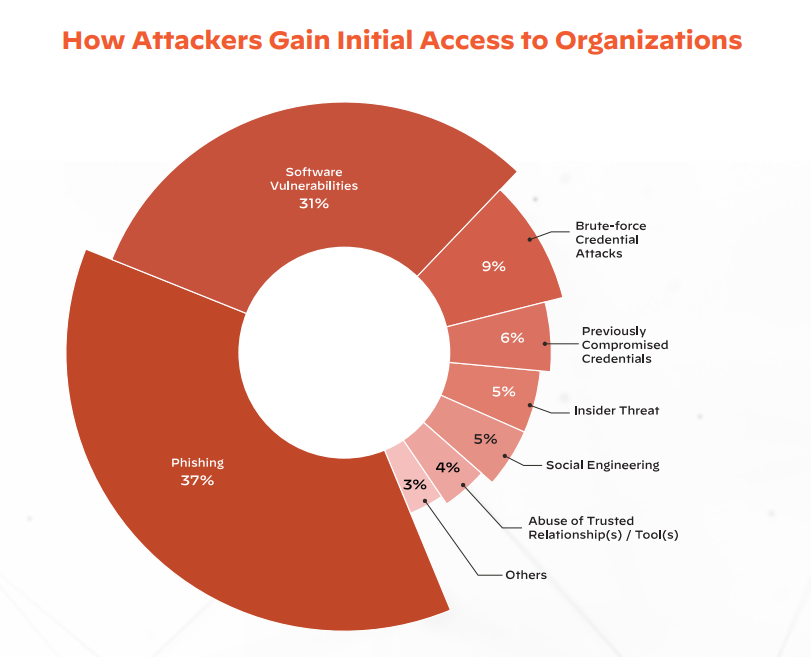
For what seems like forever now, we have been hearing that email is the number one way in which cybercriminals gain access to private networks. The oft-quoted stat is that 99% of threat vectors worm their way in through phishing and social engineering.
We were surprised to learn that phishing, although still #1, but accounts with 37% of successful attacks. The rest:
- 31%: Software vulnerabilities,
- 14%: A combination of insider threats, social engineering and abuse of trusted relationships.
- 9%: Brute-Force Credential Attacks
- 6%: previously compromised credentials that were not changed.
The diagram below, Palo Alto’s Unit 42 Research Shows How Attackers Gain Initial Access to Organisations.
Obviously, things are changing more rapidly than the speed of sound. Just in case anyone is having trouble keeping up, and borrowing heavily from our partner, Palo Alto’s e-book, here are five key topics that CISOs should understand inside and out.
Supply Chain Attacks
With increasingly distributed networks, and hybrid working a fact of life today, organisations are routinely creating virtual spaces in which stakeholders can work collaboratively. All to the delight of cybercriminal enterprises, because once entry is gained into one corporate portal, the marauders can hop, skip and jump their way seamlessly into the networks of other connected organisations.
The result is that multi-stage, multi-vector attacks have become the norm.
Today, it’s also highly possible that one of the stakeholders with whom you collaborate regularly, or one of the firms within your supply chain, manufacturers its products offshore.
One of these companies may do business with a company in Russia, Iran, North Korea or China (the top sources of nation-state threat activities, according to Microsoft’s Digital Defense Report 2022). Now, your network could be vulnerable to a nation-state threat vector. All it takes is the smallest of security shortcomings somewhere along the line, for a massive problem to be unleashed. It’s akin to a small ocean wave encountering interference of some kind and being transformed into a rogue wave, which can be highly destructive.
This has become so problematic that many insurance companies no longer cover nation-state attacks, likening them to acts of war, which are not covered by most policies.
The Solution: Embed Security into the Software Development Pipeline.
MFA can also help, which leads us to number two.
Multi Factor Authentication
Thi s is an excellent first line of defence – provided you use it, of course. According to Unit 42 2023 research, “89% of the organizations that fell victim to business email compromise (BEC) attacks had failed to turn on MFA or follow email security best practices. Additionally, in 50% of all Unit 42 incident response cases— BEC or otherwise—organizations lacked MFA on key internet-facing systems such as corporate webmail, virtual private network (VPN) solutions, and other remote access solutions.
The Solution: Integrate MFA for all remote access, internet-accessible, and business email accounts to greatly reduce your organization’s attack surface. To prevent threat actors from circumventing MFA, disable legacy authentications/ protocols and confirm that MFA is not only deployed, but that employees are also using it correctly, and avoid using SMS as a second form of authentication.
Cloud Security and Identity and Access Management (IAM)
Improperly configured cloud environments essentially leave the door unlocked for malicious actors, allowing them to gain initial access without needing to find and exploit a vulnerability or make use of sophisticated techniques. It’s no surprise that attackers commonly look for improperly configured cloud environments.
The Solution: Secure Your Cloud Environments with Proper Training and Configuration. Access to cloud controls such as Cloud Services Provider (CSP) consoles, APIs, and command-line interfaces in the cloud should be restricted to only those who need it.
Growing Attack Surfaces
Modern attack surfaces are inherently dynamic, and constantly shifting, moving and growing over time. This means that as attack surfaces grow, the number of unmanaged assets across those surfaces grow, too. As a result, attackers are becoming increasingly adept at scanning the internet in search of vulnerable systems and exploiting gaps in security before they can be patched.
The Solution: Conduct an attack surface audit, implement the changes needed, they consider using an attack surface platform (Think: “as a Service”).
Overloaded IT teams
In 11% of Unit 42 incident response cases, important security alerts got lost without sufficient review/action. Also problematic: Poor processes for patch management tasks contributed to threat actor success in 28% of instances.
The Solution: Intelligent automation can help your team prioritize scarce resources, consolidate visibility and control over a dynamic network, and reduce response and recovery tasks.
As you can see, cyber security isn’t the job of one person. It’s a team sport where the good guys have to wok together to vanquish the cyber villains. If you ‘d like us to join your team and fight for you, please contact us:[email protected], or call 1.877.238.9944, to arrange a time to discuss your needs.











